Privileged Access Management
PAM Solution
SWAWE PAM
Privileged Access Management (PAM) est aujourd’hui un pilier essentiel de la cybersécurité et de la conformité des environnements SAP.
Avec SWAWE PAM, vous maîtrisez, contrôlez et tracez l’ensemble des accès à privilèges élevés, tout en permettant à vos équipes IT d’intervenir rapidement en cas d’urgence.
Réduisez les risques, sécurisez les accès critiques et répondez efficacement aux exigences des auditeurs.
Une gestion dynamique et sécurisée des accès à privilèges
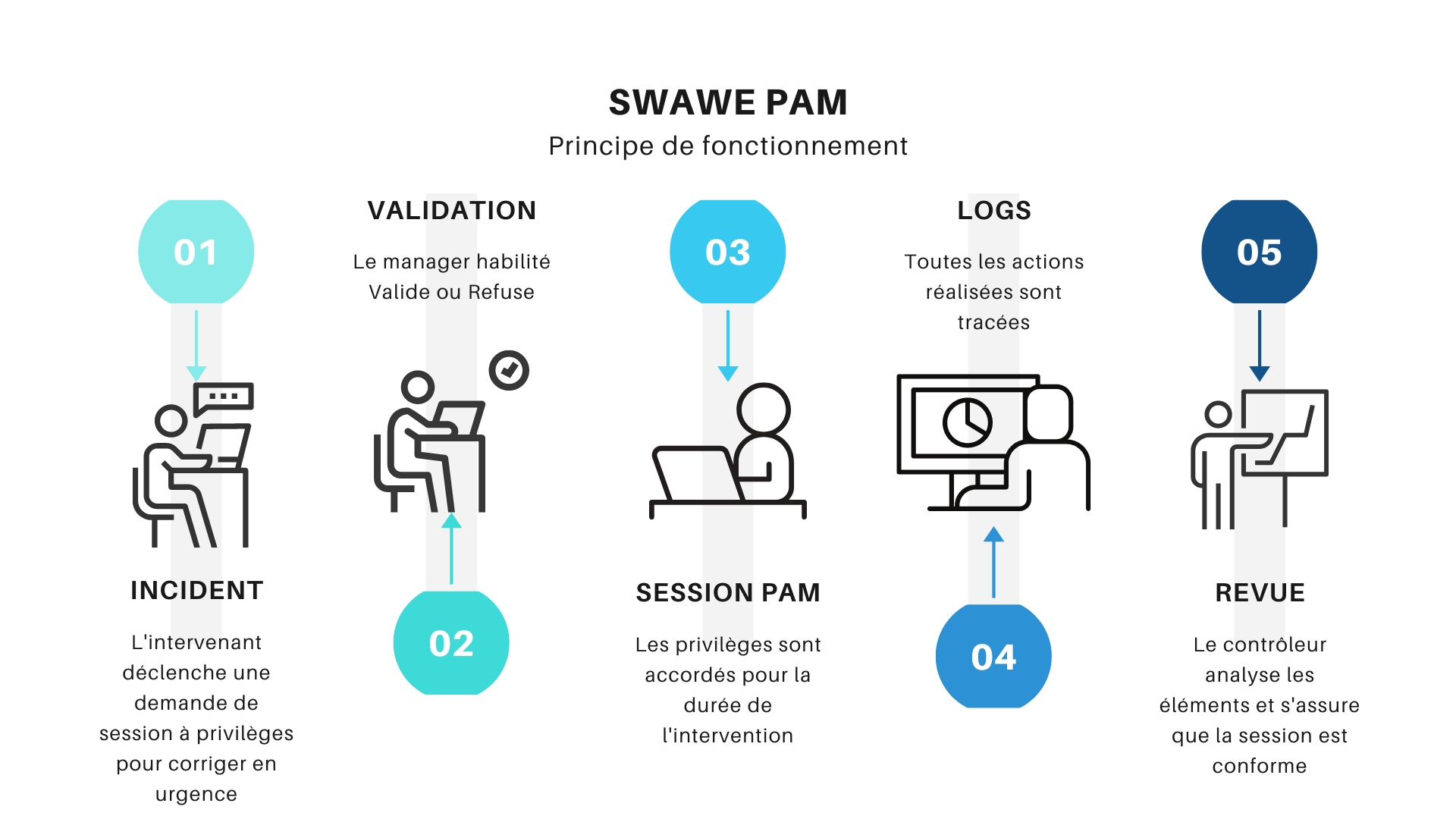
Le fonctionnement de SWAWE PAM repose sur un principe simple mais structurant : les utilisateurs n’ont jamais de droits excessifs par défaut, mais peuvent y accéder de manière contrôlée lorsque cela est nécessaire.
Concrètement, un utilisateur SAP conserve son rôle standard au quotidien. Lorsqu’il a besoin d’effectuer une action sensible, il formule une demande d’accès à privilèges via la solution. Cette demande peut être automatiquement validée selon des règles définies, ou soumise à un workflow d’approbation.
Une fois l’accès accordé, celui-ci est limité dans le temps et dans son périmètre. Toutes les actions réalisées sont alors enregistrées avec précision. Cette approche permet d’assurer un haut niveau de sécurité tout en maintenant la fluidité des opérations IT.
SWAWE PAM ne se contente donc pas de gérer des droits : il orchestre un véritable cycle de vie des accès à privilèges, depuis la demande jusqu’à l’audit.
Main benefits:
A PAM process under control
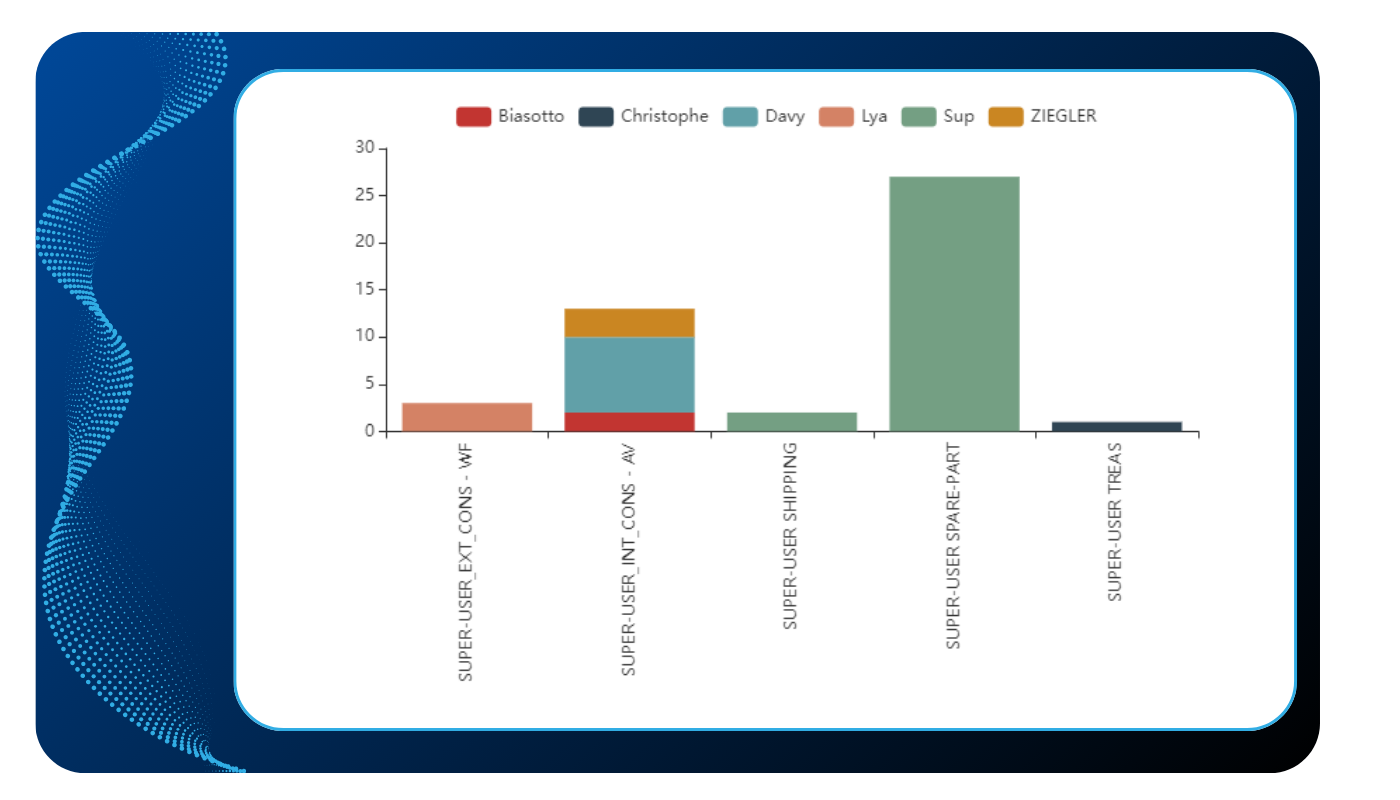
A first check is carried out when proposing the extended roles to the superuser requester. This role limitation is defined according to the organization to which the applicant is attached.
Then, to further secure this process, you can set up a validation workflow by a manager.
All actions performed through the superuser are traced, historized and auditable.
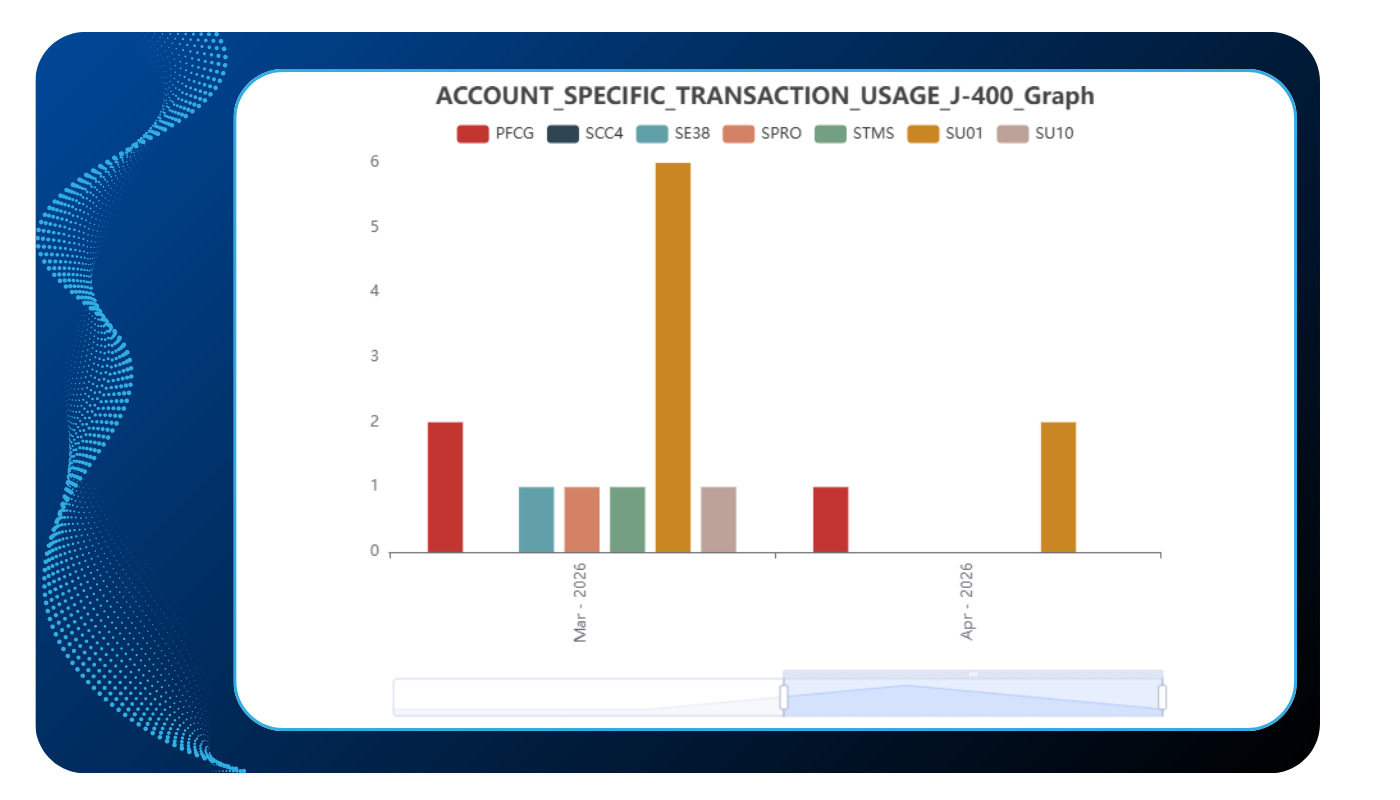
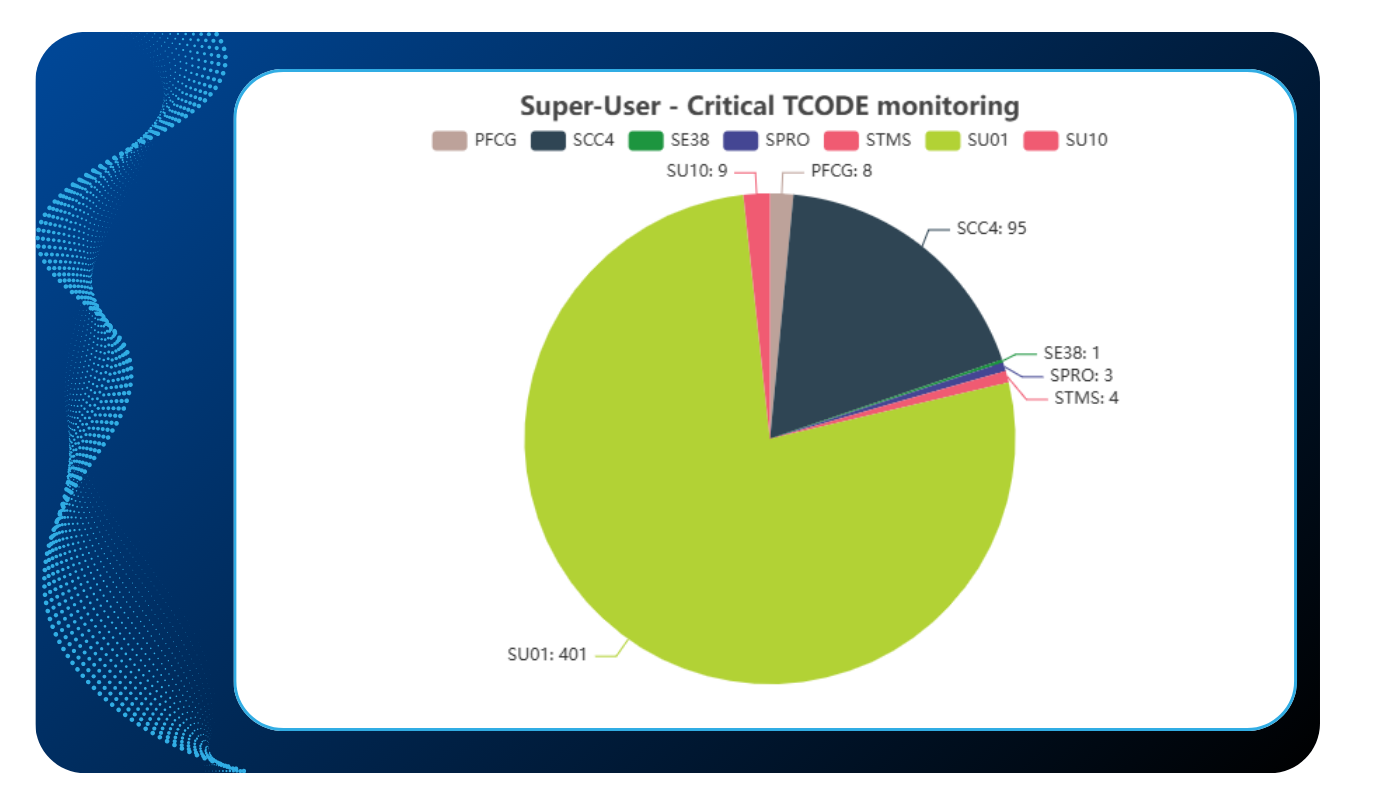
Reports and graphs make it possible to have a synthetic vision on the use of the super-user: who used it? What transactions were executed? Which information have changed? Period of use? How many times?
Continuous control of access to privileged accounts
All tasks related to the use of the super-user are stored in SWAWE. These are therefore auditable and we can find the name of the participant, the purpose of his request, the name of the validator, the transactions actually executed and the modified data. Reports and dashboards provide a synthetic view of the number of requests, who uses them, the transactions executed...
Principales fonctionnalités de la solution
SWAWE PAM :
Des tableaux de bord orientés décision
SWAWE PAM met à disposition des tableaux de bord qui ne se limitent pas à une simple visualisation technique. Ils permettent de comprendre l’usage réel des accès à privilèges, d’identifier les tendances et de détecter les points de vigilance.
Les équipes IT, sécurité ou conformité peuvent ainsi suivre l’activité des comptes sensibles, analyser les transactions critiques et produire des rapports adaptés à leurs enjeux. Cette capacité d’analyse transforme la gestion des accès en un véritable outil d’aide à la décision.
Access to logs
Cette transparence est essentielle pour démontrer la conformité, mais aussi pour instaurer un climat de confiance entre les équipes métiers, IT et audit. Chaque intervention est documentée, vérifiable et exploitable.
Reprenez le contrôle de vos accès à privilèges SAP
Sécurisez les accès sensibles, encadrez les élévations de droits et assurez une traçabilité complète avec une solution de Privileged Access Management (PAM) pensée pour SAP.
Demandez une démonstration de SWAWE PAM et découvrez comment maîtriser vos accès critiques sans ralentir vos équipes.
FAQ : Questions fréquentes sur le Privileged Access Management
Qu’est-ce qu’une solution de Privileged Access Management (PAM) ?
Une solution de Privileged Access Management (PAM) est un dispositif de sécurité qui permet de contrôler, encadrer et surveiller l’utilisation des comptes disposant de privilèges élevés dans un système d’information. Concrètement, une solution PAM comme SWAWE PAM ne se contente pas de gérer des droits : elle permet de les attribuer de manière temporaire, contextualisée et tracée.
L’objectif du Privileged Access Management est de limiter les risques liés aux accès sensibles, tout en conservant la capacité d’intervention des équipes IT lorsque cela est nécessaire.
Pourquoi mettre en place une solution PAM dans un environnement SAP ?
Mettre en place une solution PAM dans un environnement SAP répond à un enjeu majeur : sécuriser un système qui concentre des données critiques et des processus métiers essentiels.
Une solution de Privileged Access Management permet de réduire drastiquement les droits permanents, souvent pointés lors des audits, tout en autorisant des accès exceptionnels de manière contrôlée.
Avec SWAWE PAM, les entreprises peuvent ainsi répondre aux exigences de conformité (RGPD, SOX…) tout en maintenant un haut niveau d’efficacité opérationnelle.
Comment fonctionne une solution de Privileged Access Management ?
Le fonctionnement d’une solution de Privileged Access Management comme SWAWE PAM repose sur une logique d’élévation temporaire des privilèges.
Un utilisateur conserve ses droits standards, puis demande un accès à privilèges lorsqu’une tâche spécifique le nécessite. Cet accès est accordé selon des règles définies, éventuellement validé par un workflow, et limité dans le temps.
SWAWE PAM enregistre ensuite l’ensemble des actions réalisées, garantissant une traçabilité complète. Ce fonctionnement permet de concilier sécurité, contrôle et fluidité des opérations.
Quelle est la différence entre IAM et PAM ?
La différence entre IAM et PAM est essentielle pour comprendre une stratégie de sécurité des accès.
Une solution IAM (Identity and Access Management) gère l’ensemble des identités et des droits des utilisateurs au quotidien, tandis qu’une solution PAM (Privileged Access Management) se concentre spécifiquement sur les accès les plus sensibles et à haut risque.
Autrement dit, le PAM vient compléter l’IAM en ajoutant une couche de contrôle renforcée sur les comptes à privilèges, là où les enjeux de sécurité sont les plus critiques.
En quoi une solution PAM améliore-t-elle la conformité et les audits ?
Une solution PAM améliore la conformité et les audits en apportant une visibilité totale sur l’utilisation des accès à privilèges.
Avec SWAWE PAM, chaque action est liée à un utilisateur, une demande et un contexte précis. Cela permet de démontrer facilement qui a fait quoi, quand et pourquoi.
Cette capacité de traçabilité répond directement aux attentes des auditeurs et simplifie considérablement les processus de contrôle interne, tout en réduisant les risques de non-conformité.
Est-ce qu’une solution PAM ralentit les équipes IT ?
Contrairement aux idées reçues, une solution de Privileged Access Management ne ralentit pas les équipes IT, à condition qu’elle soit bien conçue.
SWAWE PAM permet justement de fluidifier les opérations en automatisant les demandes d’accès, en réduisant les frictions et en évitant les blocages liés à des droits insuffisants ou mal attribués.
Les équipes gagnent en autonomie tout en évoluant dans un cadre sécurisé, ce qui améliore à la fois la productivité et la gestion des risques.
SWAWE PAM remplace-t-il les comptes SAP existants ?
Non, SWAWE PAM ne remplace pas les comptes SAP existants, mais vient les compléter intelligemment.
La solution s’appuie sur les rôles et comptes déjà en place, tout en encadrant leur utilisation via des mécanismes de contrôle, de limitation dans le temps et de traçabilité.
Cela permet de renforcer la sécurité sans remettre en cause l’organisation existante, ni perturber les habitudes des utilisateurs.
À quels types d’entreprises s’adresse une solution PAM comme SWAWE PAM ?
Une solution PAM comme SWAWE PAM s’adresse à toutes les entreprises utilisant SAP, mais elle prend une dimension particulièrement stratégique dans les organisations complexes ou fortement réglementées.
Les entreprises soumises à des audits fréquents, à des contraintes de conformité strictes ou à des enjeux élevés de sécurité des données trouveront dans le Privileged Access Management un levier majeur de maîtrise des risques.
SWAWE PAM est ainsi particulièrement adapté aux grands groupes, aux ETI et aux structures ayant des environnements SAP critiques.
