Identity & Access Management
Identity and Access Management
SWAWE IAM
La gestion des identités et des accès est aujourd’hui au cœur des enjeux de sécurité et de gouvernance des systèmes d’information. Dans les environnements SAP, où les données sont particulièrement sensibles, une solution IAM (Identity and Access Management) ne se limite plus à gérer des comptes : elle devient un véritable levier de maîtrise des risques et de performance opérationnelle.
Avec SWAWE IAM, vous structurez, automatisez et sécurisez l’ensemble du cycle de vie des accès. Vous gagnez en visibilité, en cohérence et en conformité, tout en simplifiant la gestion quotidienne des droits.
Solution IAM, une gestion complète du cycle de vie des identités et des accès
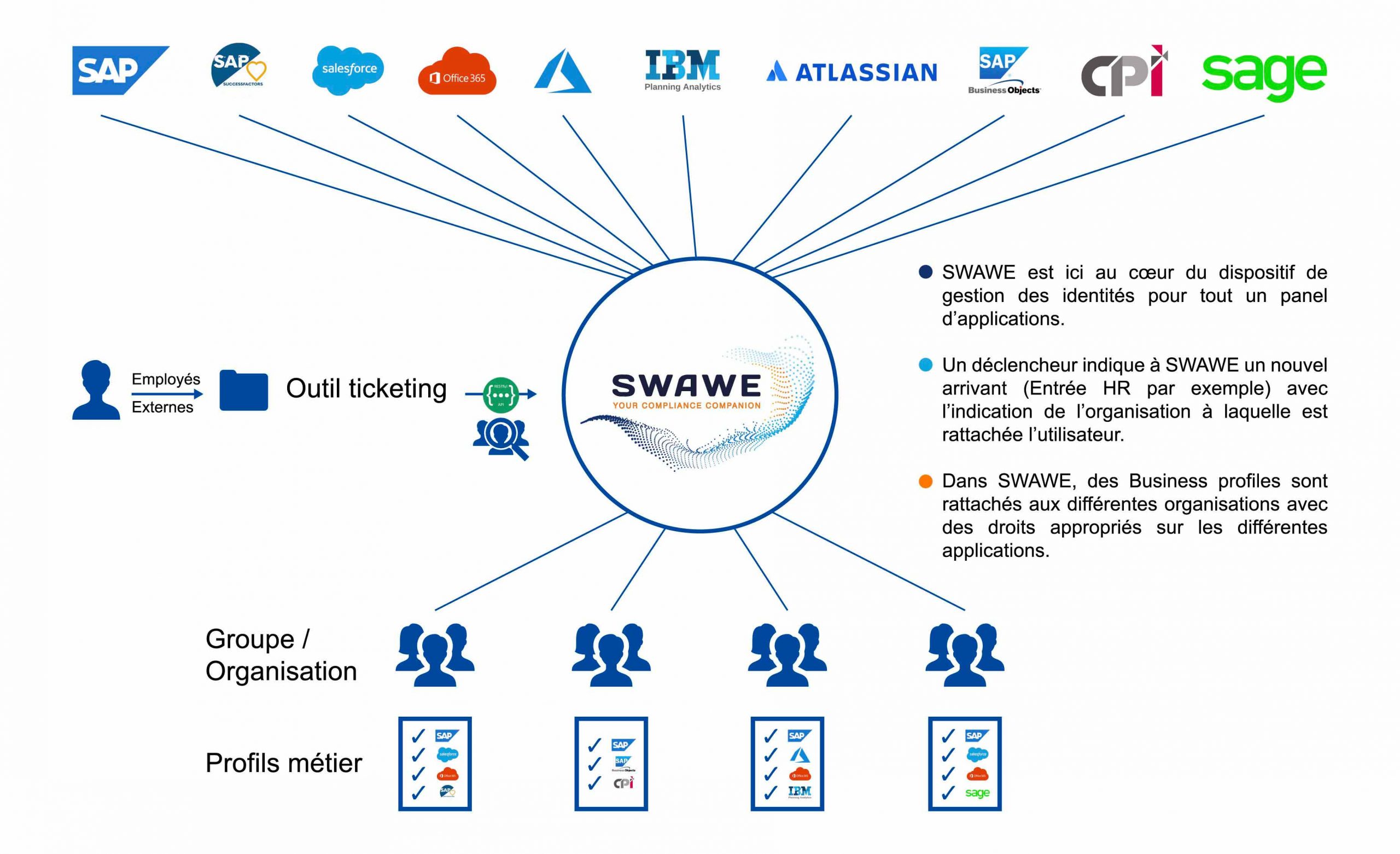
Le module de gestion des identités SWAWE IAM permet de de gérer l’ensemble du cycle de vie des utilisateurs, depuis leur arrivée dans l’entreprise jusqu’à leur départ, en passant par leurs évolutions de poste.
Lorsqu’un utilisateur rejoint l’organisation, ses accès sont automatiquement attribués en fonction de son rôle, de son service ou de sa localisation. Lorsqu’il change de fonction, ses droits sont ajustés en conséquence. Et lorsqu’il quitte l’entreprise, ses accès sont révoqués immédiatement.
Ce fonctionnement automatisé permet de garantir que chaque utilisateur dispose en permanence des droits adaptés à sa mission, ni plus, ni moins. SWAWE IAM introduit ainsi une logique de cohérence et de continuité dans la gestion des accès.

Main benefits of an IAM solution
Accurate mapping of identities and access
Integrating an IAM solution is a way to improve and automate identity management so that all of the following elements are considered: identity and authorization governance, organization and processes, data sensitivity classification, segregation of duties (SOD), and application rights provisioning.
Quality and compliance of your data
SWAWE allows you to store and log all actions related to identity management and application rights assignment. The automation of the various processes parameterized in the IAM guarantees the quality and compliance of the information contained therein.
Simplified role assignment management
Having set up in SWAWE a repository of IT applications (with authorizations by business profiles), automated validation circuits (by workflows), parameters filled in by default according to the organization of the beneficiary of the rights implicitly simplifies the management of the assignment of rights.
Main features of the SWAWE IAM solution:
Identity Management Automation
Managing and controlling the user lifecycle is often difficult because most of the time processes are done "manually" without a tool that centralizes and automates processes related to application security. SWAWE enables this automation by ensuring compliance with the approval, traceability and segregation of duties process.
Preventive risk analysis
Critical risk analysis or SOD can be done at any time in SWAWE. In the project or maintenance phase, it is sometimes useful to be able to simulate changes in rights assignments to know the impacts on risks, without actually assigning the rights. It is a preventive risk analysis.
Customizable approval workflow
To comply with best practices, it is necessary to set up a validation process when creating or updating the user file. Workflows can be defined at different levels: during the validation of the request by a manager (in connection with the attachment of the beneficiary to an organization), during the validation by a process owner risks the SoD analyses, during a validation by an additional interlocutor to complete / validate the initial request ...
Integration with your existing tools
SWAWE can be used independently, but it can also be integrated into the mapping of existing company applications. This prevents the company from multiplying its applications and thus maintaining a tool that centralizes its identities and associated application rights. Interactions from a technical point of view between the company application and SWAWE take place via APIs.
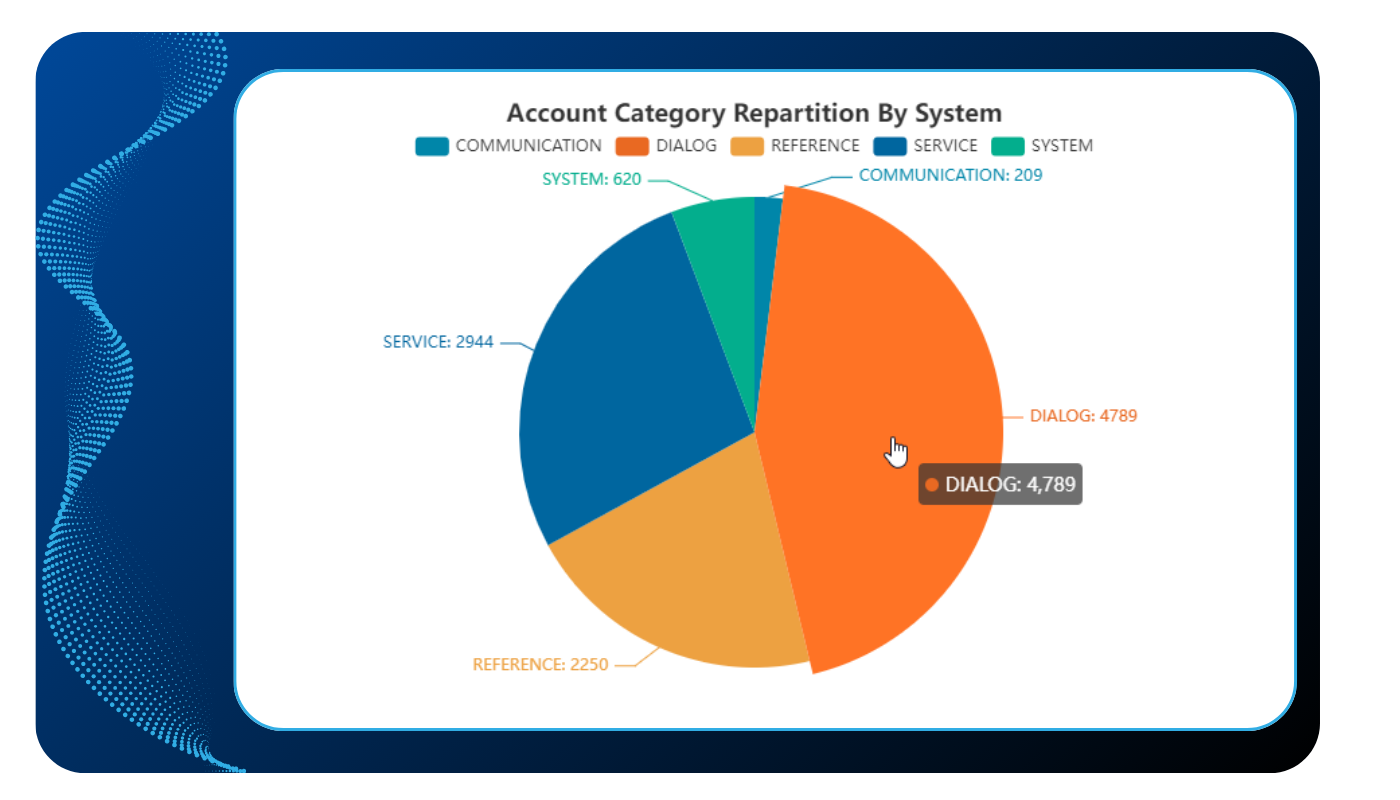
Custom reports and dashboards
SWAWE has by default a set of tables that allow you to create dashboards or reports according to the needs of the company. In the context of IAM, we can, for example, set up reports on active/inactive accounts, on the types of users, on new risks that appeared during the last creations, or create detailed lists with the use of transactions or with the details of risks or with the name of the associated business rights...
Materialization of evidence for auditors
SWAWE allows you to store and log all actions related to identity management and application rights assignment. From the request to create a user to the provisioning of it in the system, all information is traced and historized, and therefore auditable.
Reprenez le contrôle de vos accès avec SWAWE IAM
Adopter SWAWE IAM, c’est mettre en place une solution d’Identity and Access Management capable de structurer durablement votre gestion des identités et des accès.
Demandez une démonstration et découvrez comment transformer votre gestion des accès SAP.
FAQ : Questions fréquentes sur l’IAM
Qu’est-ce qu’une solution IAM (Identity and Access Management) ?
Une solution IAM (Identity and Access Management) permet de gérer les identités des utilisateurs et leurs droits d’accès aux systèmes d’information. Une solution IAM comme SWAWE IAM centralise ces प्रक्रses et les automatise afin de garantir que chaque utilisateur dispose des bons accès, au bon moment, selon son rôle.